Life cycle management lcm life cycle management is the implementation management and oversight by the designated program manager pm of all activities associated with the acquisition development production fielding sustainment and disposal of a dod system across its life cycle jcids operation manual.
Steps in the information security program life cycle dod.
What is a repository of scientific and technical documents for the united states department of defense and serves the dod community as the.
Operation of the defense acquisition process.
It is important to understand that a security program has a continuous life cycle that should be constantly.
Specified set of security requirements throughout the life cycle of the information system.
The modern day information security program has been evolving since.
The six steps of the pdlc are analyse the problem design the program code the program test and debug the program formalize the solution and maintain the program.
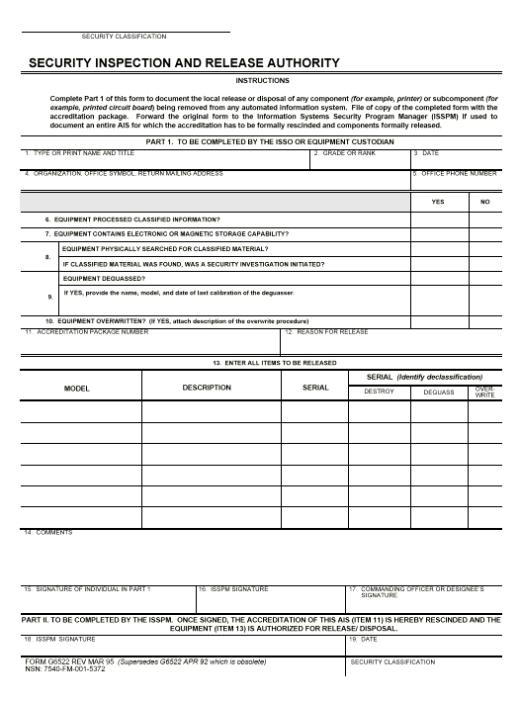
Dod information security program.
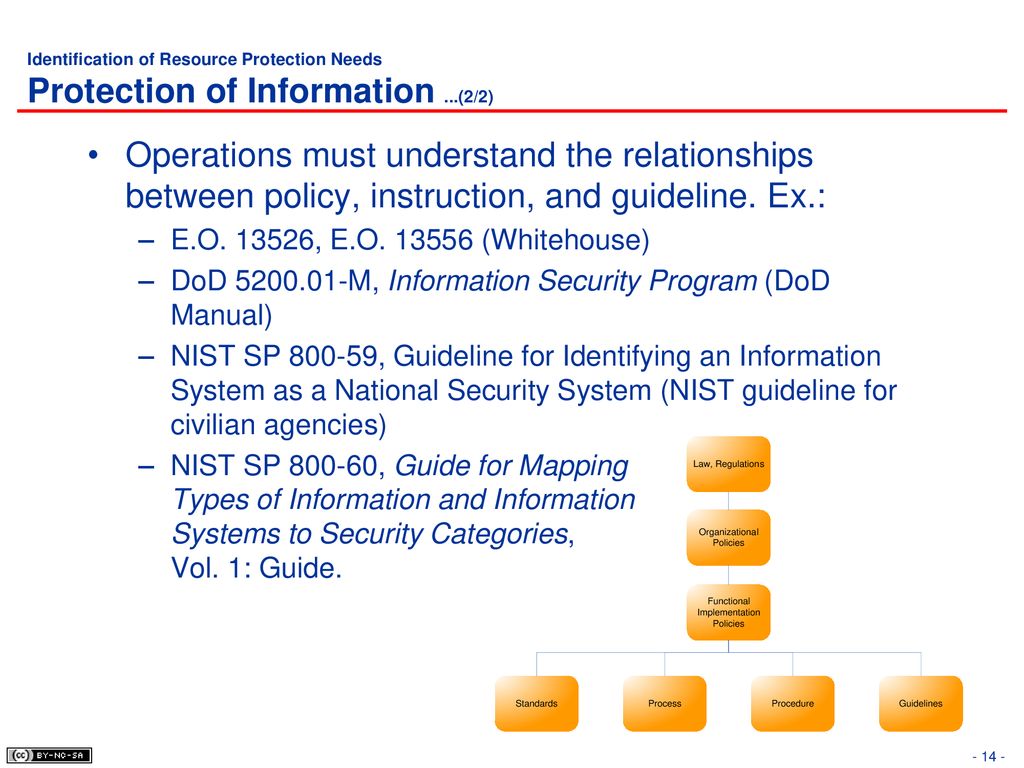
It also considers procedural physical and personnel security measures employed to enforce information security policy.
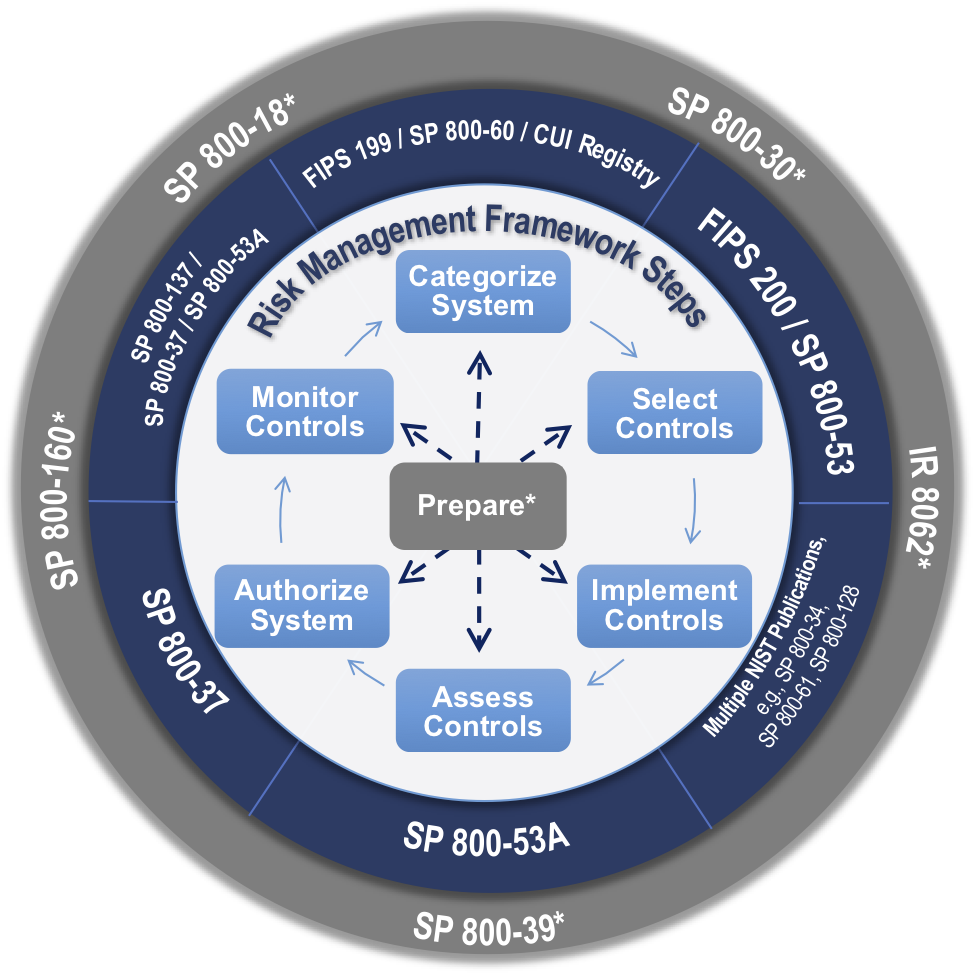
A security life cycle approach.
A information security program is the set of controls that an organization must govern.
Assigning a lower classification level to classified information because the information requires less protection in the interest of national security.
Dod information security program.
This course will provide a basic understanding of the program the legal and regulatory basis for the program and how the program is implemented throughout the dod.
Identify the feasibility of designing and developing defense exportability features def for the system.
National industrial security program operating manual nispom dod 5220 22 m.
And estimate potential.
Physical security program.
During this course you will learn about the dod information security program.
Procedures for the dod personnel security program psp usd i dod 5200 08 r.
Protection of classified information.
What are the steps of the information security program life cycle.
Classification safeguarding dissemination declassification and destruction the unauthorized disclosure of confidential information could reasonably be expected to cause to our national security.